Release 5.6.1 3 Jan 2026
This release includes the following improvements, new algorithms, translations and bugfixes:
Verification of JAR Files
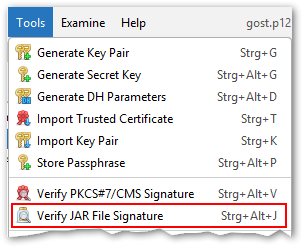
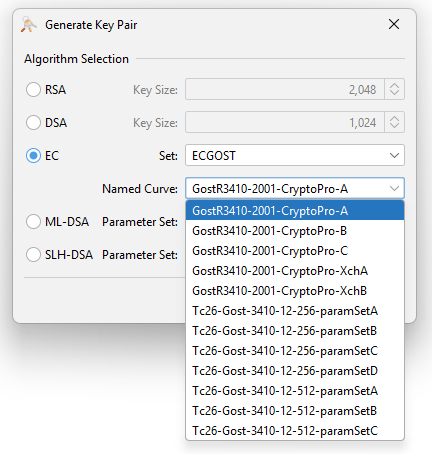
Signing JAR files has been part of KSE's functionality for a long time. Now it is also possible to verify the signatures of signed JAR files.
This can be done via the "Verify JAR File Signature" menu item in the Tools menu.
After selecting a signed JAR file, KSE will display the details of the signatures found in the JAR file and indicate whether the signatures are valid or not.
The verification details are very similar to the output of the "jarsigner -verify" command (see for example jarsigner - Example of Verifying a Signed JAR File).
The details include:
- the overall signature status
- for each file in the JAR the name, size, date and verification flags
- a button to show further details about the signatures (a JAR can have multiple signatures)
- a button to show the certificates
The meaning of the verification flags are probably already known from jarsigner but here is a short explanation (the same explanation is displayed in the tooltip when you hover over the flags column header):
- s = signature was verified
- m = entry is listed in manifest
- k = at least one certificate was found in keystore
This feature was contributed by jonwltn.
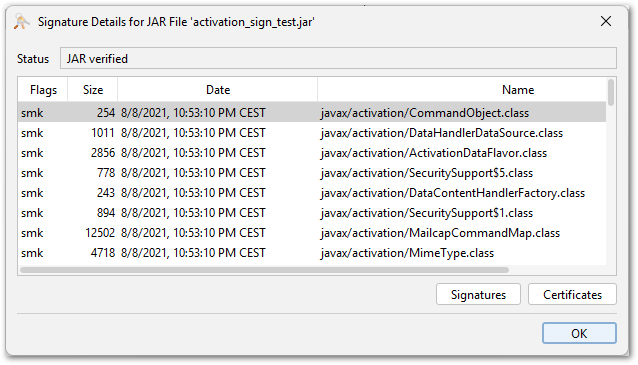
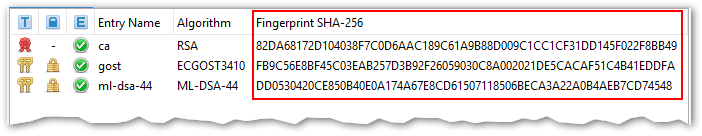
Post Quantum Cryptography (PQC) Algorithms: ML-DSA, ML-KEM and SLH-DSA
KSE now supports the ML-DSA and SLH-DSA signature and key algorithms. These algorithms are part of the NIST standardization process for post-quantum cryptography (PQC).
Supported are the following operations with these algorithms:
- key pair generation
- signing certificates, CSRs, CRLs, JARs and arbitrary files
- import and export of private and public keys
- viewing key details
In addition to that KSE also supports generating ML-KEM keypairs, but only in certificates that are signed with another key pair (as ML-KEM is a key encapsulation mechanism and not a signature algorithm). This is achieved by using the "Sign New Key Pair" feature in the context menu of a signature key and selecting ML-KEM as the key algorithm for the new key pair. The result is basically the same as using the keytool commands described in JEP 496.
This feature was contributed by AnassBousseaden (ML-DSA) and jonwltn (SLH-DSA and ML-KEM).
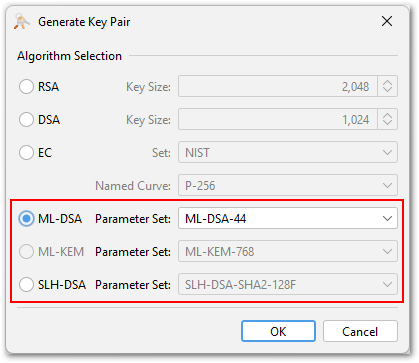
SM2 and ECGOST
KSE now supports the SM2 and ECGOST signature and key algorithms. These algorithms are widely used in China (SM2) and Russia (ECGOST). They are elliptic curve algorithms and can therefore be used by selecting the EC key type with the respective curve set in the key generation dialog.
SM2 is currently only supported for keystore files of type BKS, BCFKS and UBER.
Supported are the following operations with these algorithms:
- key pair generation
- signing certificates, CSRs, CRLs, JARs and arbitrary files
- import and export of private and public keys
- viewing key details
Contributed by jonwltn.
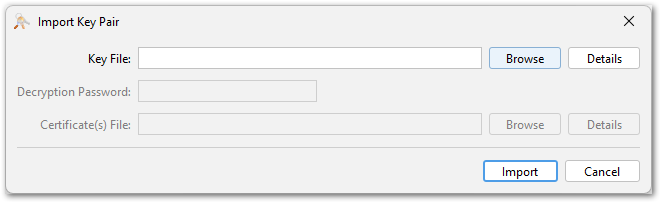
Improved Key Pair Import
In previous releases the user had to select the format of the key in the key pair import dialog, e.g. PKCS#8, PKCS#12, OpenSSL etc. Sometimes it was not clear which format to select. Or in some cases the files had a wrong file extension that did not match the actual format. This lead to confusion and import errors.
Now the key pair import dialog automatically detects the format of the key to import.
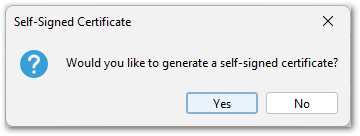
In addition to that it is now possible to import key pairs without a matching certificate. In Java keystores key pairs are always associated with a certificate chain. But if the key pair has no certificate yet, KSE now creates a self-signed certificate automatically during the import process.
If you leave the certificate fields empty and click the "Import" button, KSE will ask whether a self-signed certificate should be created.
Offering the generation of a self-signed certificate if none was provided was a contribution by Jairo Graterón.
The rework of the import dialog to use automatic format detection was contributed by jonwltn.
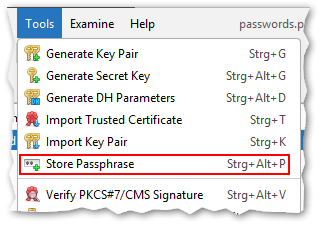
Store a Password in a KeyStore
With keytool you can store arbitrary passwords/passphrases in a keystore using the "-importpass" command. KSE now supports this feature as well.
The passphase entries can be created via the "Store Passphrase" menu item in the "Tools" menu. They are stored as secret key entries in the keystore using a "PBE*" algorithm.
The stored passphrase can be viewed and modified like normal secret key entries.
This feature was contributed by jonwltn.
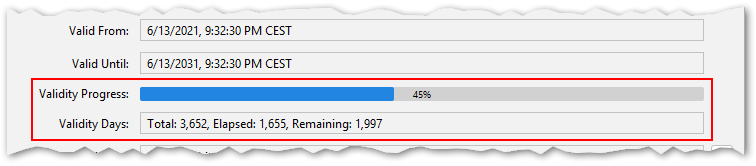
Certificate Validity Information
The certificate details view now includes two additional fields:
- a graphical representation of the certificate validity period in the form of a progress bar
- the total, elapsed and remaining days of the validity period
This feature was contributed by Jairo Graterón.
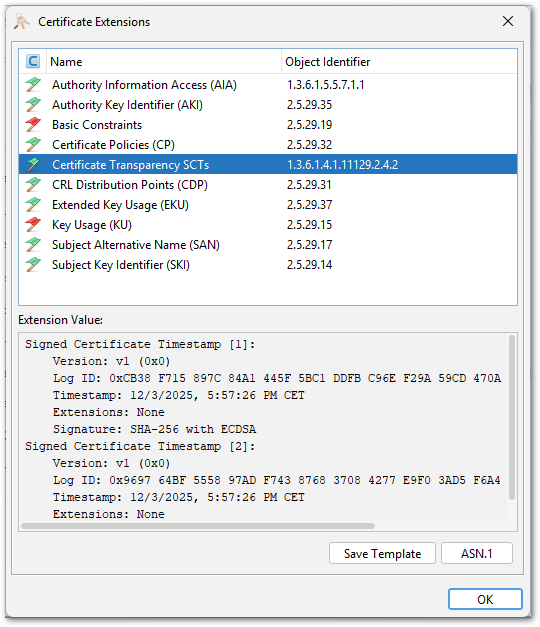
Support for Additional Extensions in Certificate Viewer
The values of the following certificate extensions are now displayed in the certificate details view:
- SignedCertificateTimestampList/SCTs (OID 1.3.6.1.4.1.11129.2.4.2)
- MS Application Policies (OID 1.3.6.1.4.1.311.21.10)
- MS NTDS CA Security (OID 1.3.6.1.4.1.311.25.2)
- MasaURL (OID 1.3.6.1.5.5.7.1.32) defined in RFC 8995
Parsing of the SCTs extension was contributed by Jairo Graterón and the other three extensions by The-Lum.
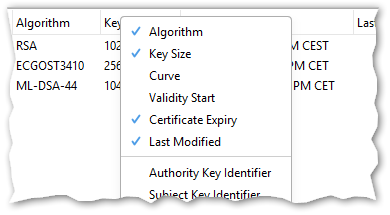
Quick Selection of Columns in Main Table
In previous releases the columns displayed in the main table could be selected in the preferences dialog. Now there is a second, quicker way to select the columns via a context menu in the table header
Right-clicking on the table header opens the context menu. It shows a list of all available columns to select or deselect them.
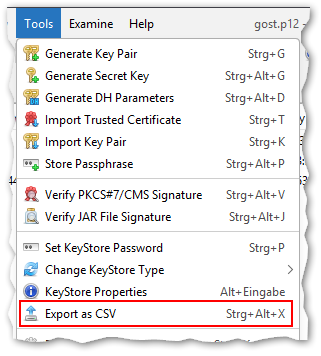
Export Main Table as CSV
The visible content of the KSE main table can now be exported as a CSV (comma-separated values) file.
This can be done via the "Export as CSV" menu item in the "Tools" menu. The exported CSV file includes all visible columns - to add or remove columns, use the column selection feature.
The separator character (either comma or semicolon) is automatically selected based on the system locale.
This feature was contributed by jonwltn.
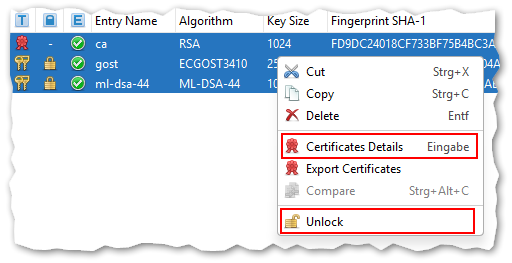
UI/UX Enhancements
The context menu for multi-selections in the main table has received the following improvements:
- The certificate details view can now be opened for multiple selected certificates at once (contributed by Jairo Graterón).
- The Unlock option is now also available for multiple selected entries (contributed by jonwltn).
- Separators have been added to improve menu organization (contributed by jonwltn).
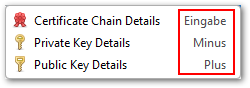
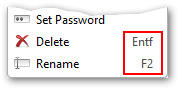
Additional keyboard shortcuts have been added to the menus (both new and existing):
- View public key details: +
- View private key details: -
- View certificate details: Enter
- Delete selected entries: Del
- Rename selected entry: F2
Contributed by The-Lum.
Action Buttons ("Import", "Export", "PEM", "ASN.1") in Dialogs:
- The order of the buttons has been standardized across all dialogs for better consistency.
- Missing buttons have been added where appropriate, e.g. "Export" in Public Key Details dialog or "PEM" in CRL Details dialog (contributed by jonwltn).
- Separators have been added to create a grouping of the buttons, because some dialogs have up to six action buttons and quickly finding the right one becomes challenging.
- The certificate extensions viewer now has a "Copy" button for putting the extension value into the system clipboard (contributed by Jairo Graterón).

The following user choices are now remembered over restarts of KSE:
- Certificate validity for generating a new key pair
- Certificate validity for signing a CSR
- CRL validity (only for new CRLs as the validity is otherwise determined from the last CRL)
- Signature algorithm
Contributed by jonwltn.
Other Enhancements
- Show certificate fingerprint in overview table (contributed by idvolkov)
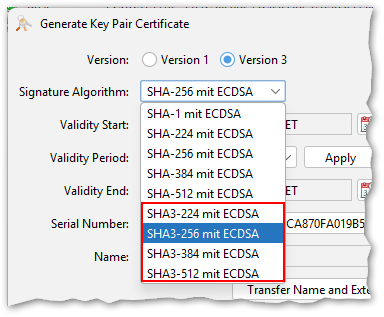
- SHA-3 with RSA PKCS#1 v1.5, RSA PSS and ECDSA signature algorithms (contributed by jonwltn)
- Support Brainpool curves in P12/JKS/JCEKS keystores (contributed by beth-soptim)
- Additional generation methods for Authority (AKI) and Subject Key Identifiers (SKI) (contributed by jonwltn)
- Export Ed25519 private key as JWT (contributed by jonwltn)
- JWS verification with Ed25519 public keys (contributed by jonwltn)
- Only show secret key algorithms based on keystore support (contributed by jonwltn)
- Implemented case-sensitive alias by key store type (contributed by jonwltn)
- Improved display of ':' in Extension viewer (contributed by The-Lum)
- Improved display of '=' and fixed 'IMPLICIT:' in ASN.1 viewer (contributed by The-Lum)
- Added CertificatePolicies OIDs of CA/Browser Forum (contributed by The-Lum)
- Added CertificatePolicy OIDs of Google (contributed by The-Lum)
- Added CertificateTransparency OID (contributed by The-Lum)
- Allow use of the verify actions without opening a key store (contributed by jonwltn)
- Added ML-DSA OID for ASN.1 view, fix minor issue on UI labels for ML-DSA PublicKey (contributed by The-Lum)
- Removed sorting of General Names (SAN, AKI, IAN, CDP) (contributed by idvolkov)
- Improved OID list for ASN.1 view (`ValidityModel`, `PkixQCSyntax-v2`, ...) (contributed by The-Lum)
- Keep leading zeros for secret keys in hex string (contributed by jonwltn)
- Added password manager KDF iteration settings in preferences
- Added progress dialogs for de-/encrypting keystore passwords
- Allow leading spaces in PEM data for "Examine Clipboard" (contributed by tenpertur)
- In CRL view the serial numbers of the revoked certificates are now displayed in a monospace font (contributed by Jairo Graterón)
- Use of "strong" secure random implementations: in the java.security file the parameter "securerandom.strongAlgorithms" can be set to define a list of known strong implementations, KSE uses this setting now and allows to select the previous behaviour in the "User Interface" section of the preferences dialog (contributed by beth-soptim).
- Added "Description" and "Role" attributes in DN chooser (contributed by Jairo Graterón)
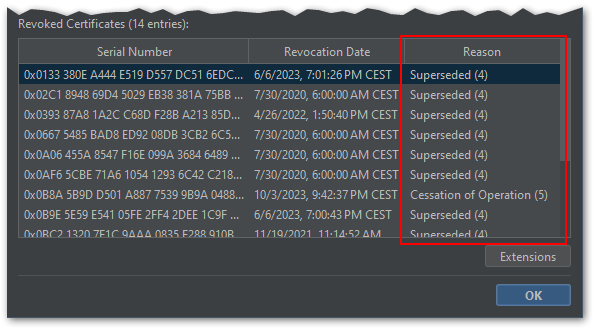
- Improved CRL revocation reason text format in CRL view (contributed by The-Lum)
Bugfixes
- Fixed signing JWT with Ed25519 (contributed by jonwltn)
- Fixed signature algorithm selection providing invalid options for EC keys (contributed by idvolkov)
- Fixed "Assistive Technology not found" error by adding accessibility module
- Fixed "internal inconsistencies" warning displayed by jarsigner (contributed by jonwltn)
- Fixed AccessDenied error when signing JAR file using output file prefix or suffix (contributed by jonwltn)
- Fixed certificate chain validation (contributed by Jairo Graterón)
- Fixed CRL verification when using BC provider (contributed by jonwltn)
- Fixed duplicate shortcut Ctrl+Alt+S (contributed by The-Lum)
- Fixed KeyStore table translations (contributed by jonwltn)
- Fixed lost focus on Secret Key entry after viewing details (contributed by jonwltn)
- Fixed key stores not being updated after expiry warning days change (contributed by jonwltn)
- Fixed private key fields button greyed out for Ed keys in JDK keystores
- Fixed wrong language being used in PubKey details fingerprint algorithm
- Keep leading zeros for secret keys in hex string (contributed by jonwltn)
- Don't ask for entry password for PKCS#12 key stores (contributed by jonwltn)
Translations
- A translation to Finnish has been started by Ricky Tigg and the current state is included in this release.
- Several other translations were started on Weblate as well but are still in a very early stage. That's why they are not included in this release yet.
- Many additions and improvements of the French translation were contributed by The-Lum
- Many additions and improvements of the Spanish translation were contributed by Jairo Graterón
Packaging
- macOS/Windows: Upgraded included Java runtime to version 25
- Java 17 is the new minimum runtime version
- macOS: The Vaqua theme is now included again.
- Third-party libraries have been updated to their latest versions; BC is now at version 1.83
Release 5.6.0 17 May 2025
This release includes the following new features, enhancements, translations and bugfixes:
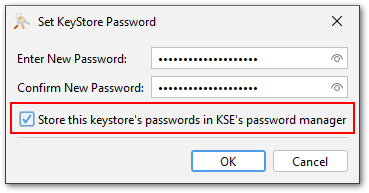
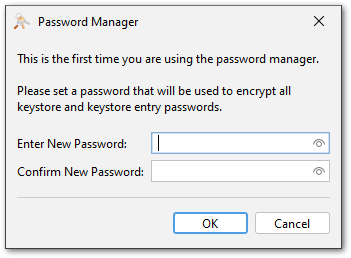
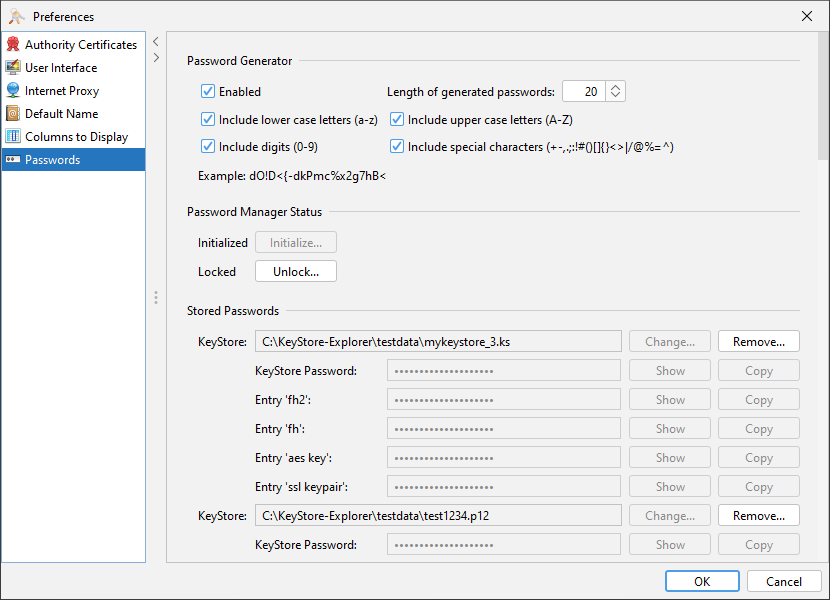
KeyStore Password Manager
The KeyStore password manager is a new feature that allows to store and manage passwords for keystore files. In combination with the new password generator it is now very easy to create and open keystores without having to type long passwords.
The password manager can be used by selecting the checkbox "Store this keystore's passwords in KSE's password manager" when creating a new keystore or opening an existing one. This decision is on a per-keystore basis and it includes all passwords of this keystore, but it can be changed later.
On the first use of the password manager, a global password for the password manager must be set. This password is used to encrypt the passwords stored in the password manager.
In the preferences dialog a new section has been added for the configuration of both the password manager and the password generator.
In the next releases, more configuration options for the password manager will be added.
Details about the password manager can be found in the documentation.
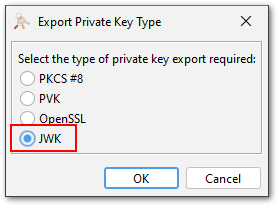
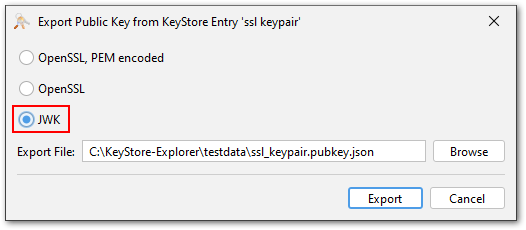
Key Export in JWK Format
The JSON Web Key (JWK) format is a JSON representation of cryptographic keys. It is defined in RFC 7517 and is used in many modern web applications.
KSE can now export public and private keys in JWK format. Supported are currently RSA and EC keys (no Ed25519).
This feature was contributed by tenpertur.
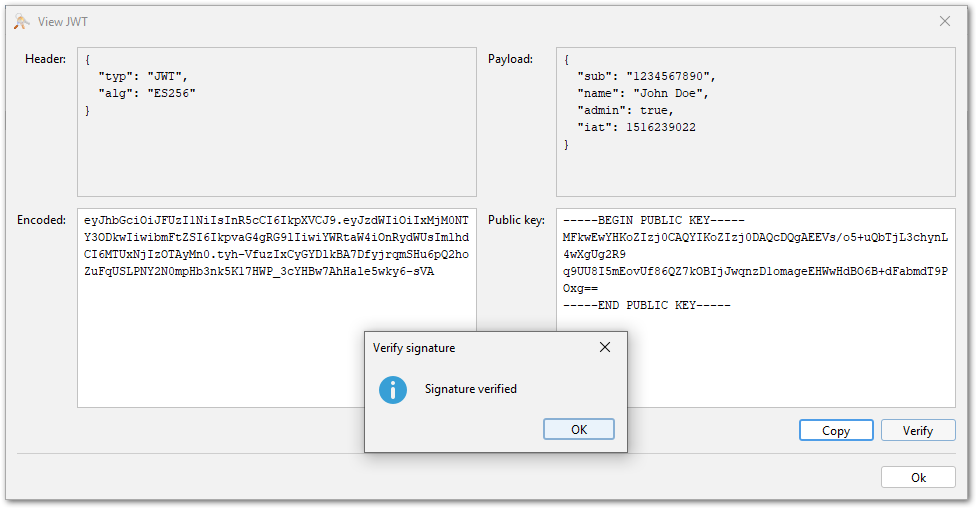
Verification of JWT Signatures
In one of the last releases, KSE introduced a viewer for JWT (JSON Web Token) files, which can be used via the "Examine File" or "Examine Clipboard" menu items.
This JWT viewer can now also verify the signatures of JWT files. This is done by pasting a public key in encoded as PEM or Base64 DER into the public key field of the JWT viewer and then clicking the verify button. Supported are RSA and EC keys and the corresponding signature algorithms ("RS...", "ES..." and "PS...").
This feature was contributed by Jairo Graterón.
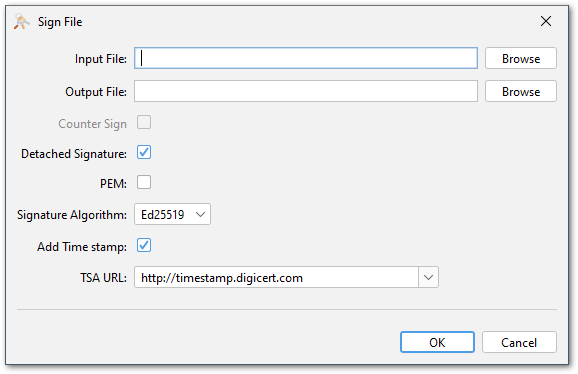
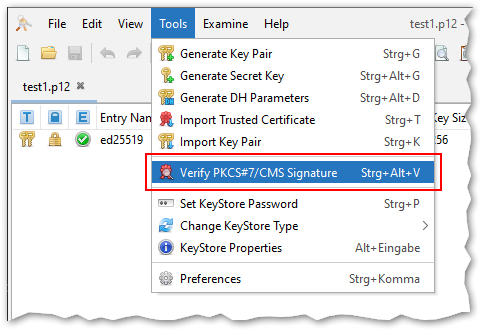
File signing and verification using PKCS#7/CMS
KSE now supports signing and verifying arbitrary files using PKCS#7/CMS. This is a widely used standard for signing files.
This feature can be found in the context menu of key pair entries:
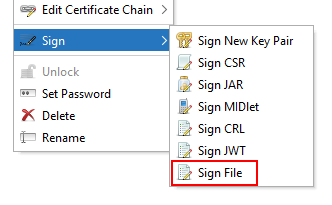
The PKCS#7 file can be either stored separately as a so-called "detached signature" or the signed file can be embedded in the PKCS#7 file. The latter is called "enveloped signature". In both cases the output format can be either PEM or binary DER.
A TSA (timestamp authority) can be used to timestamp the signature. KSE includes a list of well-known TSAs that can be used for this purpose. If you want to use another TSA, then its URL can be entered manually instead.
And finally the signature can be added as a "counter signature" to an existing PKCS#7 file. A counter signature does not sign data but another signature.
This feature was contributed by jonwltn.
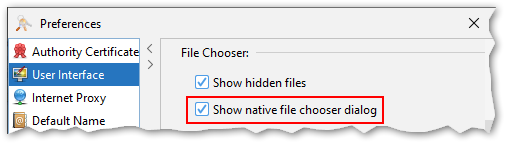
Native File Chooser
This is not really a new feature, but so far there have been several restrictions that prevented the native file chooser to be available in KSE for a majority of the users. First of all the Java runtime had to include the JavaFX library, which is not the case anymore for most modern Java distributions. Also, on macOS the native file chooser had to be disabled because of an incompatibility between tools like Karabiner or Cinch and the JavaFX library. This seems to be fixed now.
Starting with this release KSE includes the JavaFX library and the native file chooser can be enabled in the preferences.
New PKCS#12 Features
PKCS#12 is a very flexible format. It can contain an arbitrary number of key pairs, certificates and even CRLs. A wide range of encryption algorithms can be used to protect the contents of a PKCS#12 file.
With this flexibility comes complexity. There have always been compatibility issues with PKCS#12 files created by different tools. This situation has not exactly improved when Java 8 introduced support for so-called "trusted certificates" (i.e. standalone certificates that are not associated with a key in the same file) in PKCS#12 files by marking them with a custom bag attribute with OID "2.16.840.1.113894.746875.1.1".
As a result any certificate in a PKCS#12 file that is not part of the chain belonging to a key in the same file is simply ignored by the Java runtime. This has caused a lot of confusion among users.
In the meantime OpenSSL v3.2 has added a new flag "-jdktrust anyExtendedKeyUsage" to its pkcs12 command that allows to create PKCS#12 files with standalone certificates that are compatible with Java:
$ openssl pkcs12 \
-export \
-out test.p12 \
-in test.cer \
-jdktrust anyExtendedKeyUsage
$ keytool -list -keystore test.p12
Enter keystore password:
Keystore type: PKCS12
Keystore provider: SUN
Your keystore contains 1 entry
1, Jan 28, 2024, trustedCertEntry,
Certificate fingerprint (SHA-256): 52:68:B6:49:C9:8B:16:...
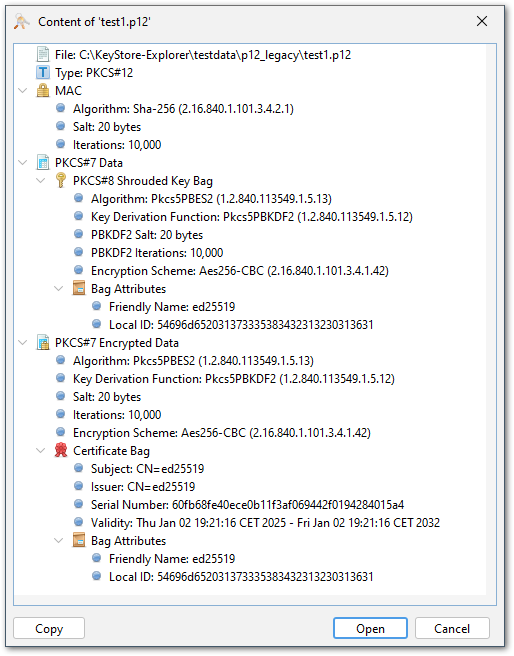
PKCS#12 Content Viewer
With OpenSSL, keytool and KSE being able to create and read PKCS#12 files with trusted certificates, there a few use cases left where KSE is not able to read certificates in PKCS#12 files created by other tools.
The new PKCS#12 viewer can be used to inspect the contents and structure of PKCS#12 files and help identify possible issues. The viewer can be opened via the "Examine File" or "Examine Clipboard" menu items. Also drag and drop of PKCS#12 files or opening them by double-clicking them in the file manager will open the PKCS#12 viewer first.
The p12 viewer shows the contents and structure of the PKCS#12 file in a tree view. The details of each entry can be viewed by expanding it in the tree view. The details include the type of the entry, the algorithm used to encrypt it and the parameters. Keys and certificates are not included, just some information like subject/issuer and serial number to identify them.
For p12 files that cause issues in KSE, the viewer might help to identify the cause of the problem. There is a "Copy" button that copies the visible structure as text to the clipboard. This then can be pasted into a GitHub issue to provide the developers with the necessary information to analyse the issue.
After inspecting the contents of the PKCS#12 file, it can be opened in KSE by clicking the "Open" button.
This feature is only temporary and will either be completely removed, reworked or moved to a less prominent place. But right now PKCS#12 is a very important topic and the viewer should help a lot with it.
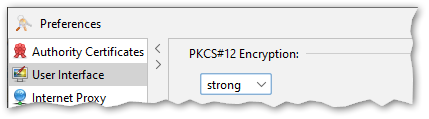
Reworked Encryption Settings for PKCS#12
The encryption settings for PKCS#12 files introduced in KSE v5.5.2 have been reworked. The previous implementation in some cases required a restart of KSE to take effect. The new implementation works reliably without a restart. Note that this setting is only used when creating a new PKCS#12 file.
Same Password for Whole PKCS#12 Content
Internally PKCS#12 files consist of "bags" that contain certificates or keys. Each key bag can be encrypted with a different password. This matches the KeyStore API which allows to use different passwords for each entry in a KeyStore. However, the widely established convention is to use the same password for all bags in a PKCS#12 file.
KSE now uses the same password for all entries when a PKCS#12 keystore is created or modified. When a PKCS#12 keystore is opened, KSE will try to use the keystore password for all entries. Only if this fails, KSE will ask for an entry password.
New Configuration System
In previous releases KSE used the Java Preferences API to store its configuration. This API is not very flexible and has some limitations. For example, it is difficult to store complex configuration objects. Also, the location of the configuration differs from platform to platform. On Windows it is stored in the registry, on macOS in a plist file and on Linux in a hidden directory in the home folder. This makes it difficult to share the configuration between different platforms or add a portable mode to KSE where the configuration files are stored in the same directory as KSE.
KSE now uses a custom configuration system that stores the configuration always in a file and searches for it in the following locations in this order:
- If a environment variable "KSE_CONFIG_DIR" is set, then this path is used.
- In the same directory as the KSE program files (kse.jar etc.)
- In a OS-specific configuration folder:
- Windows: %APPDATA%/kse/
- Linux and macOS: ~/.config/kse/
The configuration is stored in a JSON file called "config.json". The configuration file is created automatically after KSE was used for the first time.
The encrypted passwords of the password manager are stored in a separate file called "keystore-passwords.json". This file is stored in the same directory as the main configuration file.
The configuration file also includes now a section for system properties. This allows to set system properties like "sun.java2d.d3d.onscreen", which fixes a rare redraw issue on Windows. There is currently no GUI for this, because it is only needed for very special use cases.
There is no automatic migration of the old configuration to the new one.

Other Enhancements
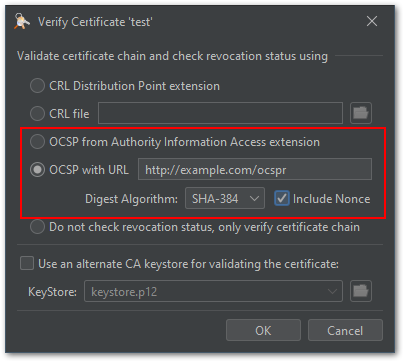
- The options for verifying a certificate have been extended to manually provide OCSP request parameters like:
- OCSP URL
- Hash algorithm
- Nonce request extension
Using the value from AIA extension instead is still possible.
This feature has been contributed by Erik Mattheis.
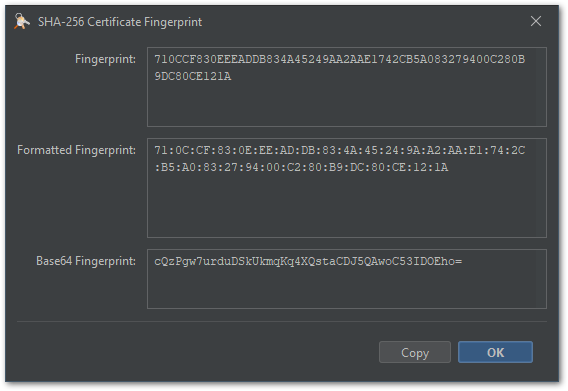
- The fingerprint views for certificate and public key fingerprints shows the value now in three different
formats:
- Hexadecimal
- Hexadecimal with a ":" as separator between the bytes
- Base64
This feature has been contributed by Jairo Graterón.
- The CRL viewer has been enhanced to show the revocation reason code. This feature has been contributed by jonwltn.
- Export of multiple certificates at once is now possible (contributed by Jairo Graterón)
- Added DESCRIPTION (OID 2.5.4.13) for DNs (contributed by Jairo Graterón)
- DH parameters are now displayed in a scrollable pane (contributed by Jairo Graterón)
- Additional file name extensions supported for "Examine Clipboard" and "Extension Viewer" (contributed by Jairo Graterón)
- Copy error message to clipboard (contributed by Jairo Graterón)
- "View Private Key" dialog now displays the original key format when examining a file or the clipboard (contributed by AndresQ)
- Improved usage of JavaFX file chooser in various ways (contributed by Colbix)
- Added keyboard support for context menu, either dedicated key or Shift-F10 (contributed by jonwltn)
- Support executing kse.sh with spaces in JAVA_OPTIONS (contributed by dadaewq)
- If the PQC algorithms that have been standardized by the NIST are used in certificates (either as signature or public key), they are now shown by their name
- Replaced Symantec's TSA with Microsoft's (due to termination of service)
- The Look&Feel can now be changed without a restart
- As a workaround for redraw issues with certain GPUs, the property "sun.java2d.d3d.onscreen" is now to "false". This can be changed - if necessary - by manually editing the config file (see above for its location and name).
Translations
- New translation: Spanish contributed by Jairo Graterón
- New translation: Russian contributed by Sergey Ponomarev
- New translation: Chinese contributed by liyansong2018
- Many additions and improvements of the French translation were contributed by The-Lum
Packaging
- macOS: Added native package for Apple Silicon (partially contributed by jonwltn)
- macOS: The Vaqua theme is not included in this release because of changes in Apple's notarization process: If jar files contain native libraries, these must be signed with an Apple developer certificate which is not the case for the Vaqua theme. If a solution is found for this problem, Vaqua will be included again in a future release of KSE.
- Linux: Added more MIME types to the kse.desktop files (contributed by Sergey Ponomarev)
- Linux: Fixed Debian package lint warnings (contributed by Sergey Ponomarev)
- macOS/Windows: Upgraded included Java runtime to version 21
- Java 11 is the new minimum runtime version
- Third-party libraries have been updated to their latest versions; BC is now at version 1.80
Bugfixes
- Fixed issue with very long OID arcs
- Fixed verify for SPKAC not working
- Fixed issue with organizationIdentifier name component
- Fixed missing curve name for non-BC EC private keys
- Fixed problem with UserNotice on CertificatePolicies extension
- Fixed restart issues
- Fixed issue with file filter when using JavaFX file chooser
- Fixed issue with switching between p12 legacy/strong encryption
Older Release Notes
KeyStore Explorer Release 5.5.0, 5.5.1, 5.5.2 and 5.5.3
KeyStore Explorer Release 5.4.0, 5.4.1, 5.4.2, 5.4.3 and 5.4.4
KeyStore Explorer Release 5.3.0, 5.3.1 and 5.3.2
KeyStore Explorer Release 5.2.0, 5.2.1 and 5.2.2
KeyStore Explorer Release 5.1.0 and 5.1.1
KeyStore Explorer Release 5.0.0 and 5.0.1