Release 5.1.1 28 Mar 2015
KeyStore Explorer 5.1.1 is a maintenance release. It includes the following bugfixes:
- Fixed ECC not available in BKS-V1 keystores
- Fixed Linux start script, it works now if called from outside the KSE folder (ticket #12, thanks to David Harper for his contribution)
- Fixed "KeyStore Explorer.app is damaged and can't be opened" under Mac OS; KSE now requires Oracle/OpenJDK 7 or higher, it no longer works with Apple's Java 6 (tickets #13 and #16, thanks to Steve Lessard and Stefano L for reporting)
- Fixed wrong order of RDNs in extensions (ticket #14, thanks to Chris Ridd for reporting)
- Fixed typo "Cerificate Serial Number" (ticket #14, thanks to Chris Ridd for reporting)
- Fixed import of EC keys (ticket #15, thanks to Mouse for his patch)
- Updated Bouncy Castle to version 1.52 (ticket #11, thanks to based for reporting)
- Fixed focus problem in password dialog
- Added program infos for windows uninstaller
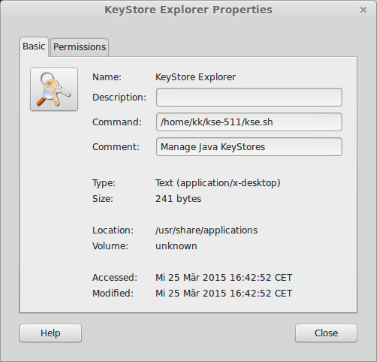
Also, the ZIP package now contains a folder with application icons in sizes from 16x16 to 128x128 pixels. Together with the fixed start script this allows for easy integration into your Linux desktop environment, like for example here in Cinnamon:
Release 5.1 02 Aug 2014
KeyStore Explorer Release 5.1 includes many new features, improvements and bugfixes.
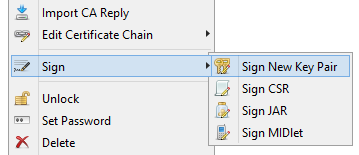
New Feature: Sign New Key Pair
This new feature makes it really easy to create complete certificate hierarchies in KSE (with root CAs, sub CAs and end entity certificates).
Prior to version 5.1 one would have to do the following steps:
- Create a self-signed root CA certificate
- Create a new key pair (which includes creating a useless self-signed certificate)
- Create a CSR from the key pair
- Sign the CSR with the CA certificate
- Import the CA reply
Since KSE 5.1:
- Create a self-signed root CA certificate
- Right click on CA certificate and select "Sign New Key Pair"
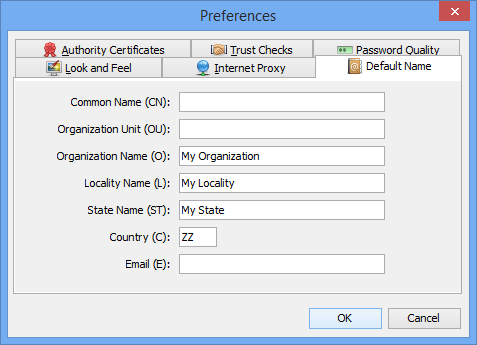
New Configuration Setting: Default Name
A new configuration setting allows to store default values for certificate distinguished names (DNs). When you create a new certificate, the input fields for Common Name, Organizational Unit, Organization etc. are pre-filled with the values from the preferences.
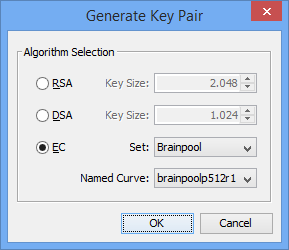
Added Support for ECC (Elliptic Curve Cryptography)
Java 7 introduced the SunEC provider for Elliptic Curve algorithms which allows keytool and jarsigner to create and use EC keys in JKS and JCEKS keystores. Third party JCE providers like Bouncy Castle have been supporting ECC in their keystore types (BKS, UBER) for some time now.
Elliptic curves are defined by a number of domain parameters. Because it is difficult to find "good" domain parameters, several organizations (e.g. NIST, SECG, ANSI, ECC Brainpool) have published domain parameters of elliptic curves for several common field sizes. These "named curves" can be referenced by name or OID.
EC key sizes are generally smaller than comparable RSA key sizes. The name usually contains the key size, e.g. "sect571k1" (571 bits) or "B-409" (409 bits).
In KSE EC key generation is done by selecting a named curve:
Which named curves are available in KSE depends on two factors: Java version and keystore type. The following table gives an overview on the available curves:
| Curve Set | Java 6 (JKS, JCEKS, P12) | Java 7+ (JKS, JCEKS, P12) | Java 6+ (BKS, UBER) |
|---|---|---|---|
| ANSI | 0 | 15 | 15 |
| SEC | 0 | 33 | 33 |
| NIST | 0 | 15 | 15 |
| Brainpool | 0 | 0 | 14 |
Added Support for Certificate Extensions and unstructuredName Attribute in PKCS#10 CSRs
Some CAs support certificate requests (CSRs) that contain X.509 extensions (for example and especially SubjectAlternativeName).
With KSE 5.1 you can create such CSRs. All you have to do is to create a new key pair, add the extensions and when exporting the CSR click the check box "Add certificate extensions to request".
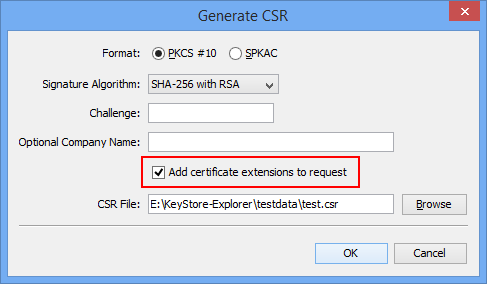
When examining CSRs in KSE it is now also possible to view the extensions.
Another addition to PKCS#10 requests is the unstructuredName attribute (see http://www.ietf.org/rfc/rfc2985.txt). In OpenSSL this is called "An optional company name" when generating requests, so KSE uses the same phrase.
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
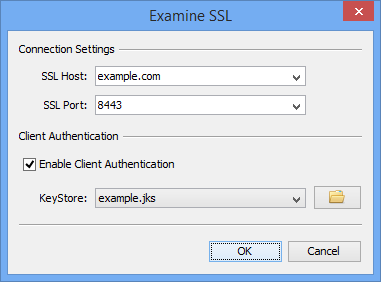
Improved "Examine SSL"
Two enhancements were made to the "Examine SSL" dialog:
- History of last used SSL hosts/ports
- SSL client authentication
Because "Examine SSL" is rarely used only once with the same server, a list of the 10 last used hosts and ports is saved between sessions. The saved hosts and ports can be selected via a drop down box.
The new feature "SSL client authentication" is useful for testing keystores. You have just to select a keystore and the private key from keystore is used to authenticate against the SSL server. If there is more than one private key in the keystore that could be used for client authentication, then standard Java mechanisms are used to find the right one.
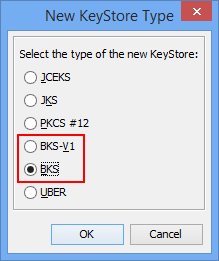
New KeyStore Type BKS Version 2
The keystore type BKS had been changed in Bouncy Castle version 1.47. This new version of BKS was incompatible, so with the release of Bouncy Castle version 1.49 BKS-V1 was re-introduced as an additional store type.
Older versions of KSE always generated BKS-V1 keystores. KSE 5.1 can generate and process both versions of BKS.
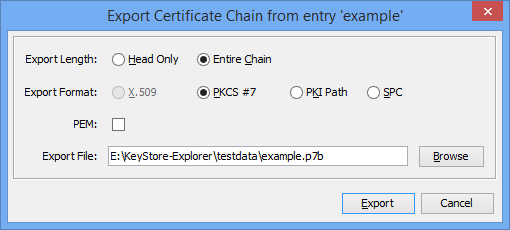
Filename Suggestions
In dialogs that include an input field for a file name (like all the export dialogs or "Generate CSR" or "Sign Jar"), this input field is pre-filled with a suggestion for the file name and path. The path suggestion is determined by either input files or last used path. The file name suggestion depends on factors like the alias of the keystore entry or the name of an input file and the type of file.
For example when you want to export the certificate chain of an keystore entry with alias "example", current working directory is "E:\KeyStore-Explorer\testdata\" and you choose PKCS#7 as export format, then "E:\KeyStore-Explorer\testdata\example.p7b" is suggested.
New Packaging and Local JRE
The redundant distribution packages kse-X-install.tar.gz and kse-X-manual.zip have been combined into kse-X.zip. This ZIP file contains (in addition to the content of the old ZIP file):- kse.sh - Shell script from .tar.gz for Linux, Solaris, Mac OS X etc.
- kse.exe - Executable for Windows
Both the shell script and the exe first search for a local Java Runtime Environment (JRE), i.e. a directory with name "jre" in the KSE directory. If it exists, the JRE in it is used for running KSE. This allows to use another JRE for KSE than the default system JRE, which is useful for example if you have to use IBM JDK, which is not compatible with KSE.

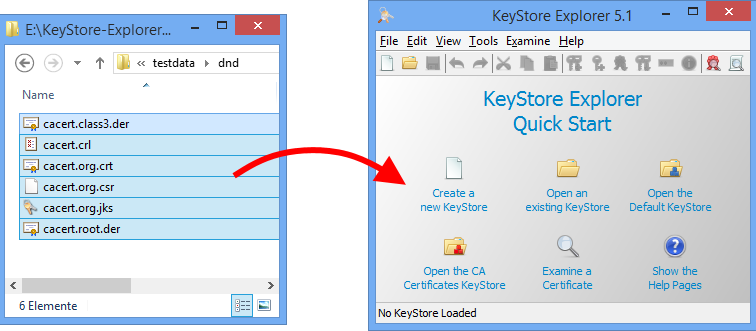
Improved Drag&Drop
In previous versions of KSE only keystores could be opened by drag&drop. In KSE 5.1 this also works for certificates, CSRs and CRLs.
If you drag&drop multiple files at once on the KSE window, then all of them are opened one after the other.
Other changes
- Added links to theSourceForge project site, the bug reports and the user discussion forum to menu "Help -> Online Resources"
- Added new secret key algorithms: ChaCha, Threefish and XSalsa20
- When copying a key pair from a PKCS#12 store type to any other store type, a reminder is shown that the password for the key pair is set to 'password'
- ASN1 dump view is now non-modal, allowing to compare ASN1 dumps
- Updated to Bouncy Castle 1.50
- Fixed bug: export multiple certificates
- Fixed NPE in import function of certificate view when user cancels new keystore dialog
- Fixed problem with pinning KSE to taskbar under Windows 8.1 and newer Java versions
Older Release Notes
KeyStore Explorer Release 5.0 and 5.0.1